The Remote Desktop is an irreplaceable device for Windows Server directors, encouraging remote access and administration. In any case, the default impediment on synchronous Remote Desktop Convention (RDP) sessions can block the productivity of server organization. This comprehensive direct points to engage directors by giving a step-by-step walkthrough on how to open the complete potential of Remote Desktop on Windows Server.
Enabling numerous RDP sessions will improve your capacity to oversee servers remotely, cultivating a more streamlined and profitable server environment. Take after along as we dive into the complexities of altering the Windows Registry, arranging Gather Approach settings, and fine-tuning Terminal Administrations to maximize the capabilities of Remote Desktop.
This prepares you with the specialized know-how and emphasizes best practices and security contemplations, guaranteeing a strong and secure usage of numerous RDP sessions.
Understanding Remote Desktop and its Limitations:
Remote Desktop, a cornerstone of Windows Server organization, empowers inaccessible access to servers for consistent administration. Despite its utility, Windows forces default impediments on the number of concurrent Remote Desktop Convention (RDP) sessions, affecting the adaptability of server organization. This segment investigates the elemental concepts of Remote Desktop and diagrams the limitations related to the default setup.
The subtleties of these impediments make it apparent why opening the capacity to have numerous RDP sessions is fundamental for upgrading productivity and efficiency in server administration. Understanding these impediments sets the stage for the subsequent steps in empowering different RDP sessions on Windows Server, whether tending to particular utilize cases or pleasing multiple directors.
Checking the Current Remote Desktop Configuration:
Before going on the trip to allow numerous Remote Desktop Protocol (RDP) sessions on your Windows Server, it is critical to review the present setup. Begin by reviewing the existing Remote Desktop settings to understand the limits given by default. Navigate to the Remote Desktop settings on your Windows Server to do so. Access System Properties by right-clicking on the This PC icon, opting for Properties, and subsequently choosing the Remote settings option. The Remote tab contains information about the current settings, including the maximum number of simultaneous RDP sessions.
Please take notice of the constraints listed and validate that they correspond with your operating requirements. This phase gives you a good picture of the beginning point and may better decide the condition of allowing numerous RDP sessions. It also acts as a critical checkpoint for identifying any conflicts or concerns that may develop during the alteration process. By inspecting the present Remote Desktop setup extensively, you create the groundwork for a seamless transition to a more dynamic and accommodating server environment.
Enabling Multiple RDP Sessions:
1. Registry Editor Modification:
Modifying the Windows Registry is one method for unlocking multiple Remote Desktop Protocol (RDP) connections. To launch the Registry Editor:
- Type “regedit” into the Run dialog box.
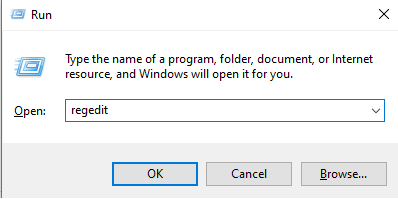
- Before you begin, make a backup of the registry.
- Discover and edit specific registry keys relating to RDP session limits.
- Change the settings associated with phrases like “fDenyTSConnections” to permit multiple sessions.
- Be cautious and exact in your updates since erroneous registry changes might cause system instability.
2. Group Policy Configuration:
Another excellent way to allow multiple RDP sessions is to use the Group Policy Editor. To access the editor:
- Go to Run dialog box and type “gpedit.msc”.
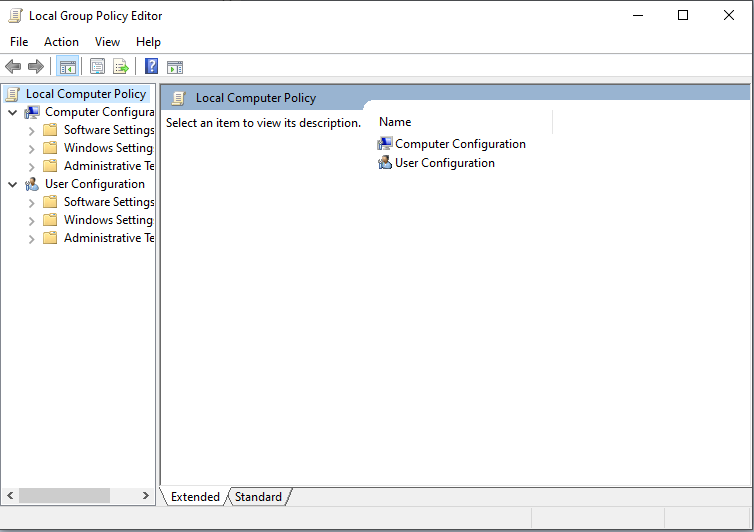
- Go to the “Computer Setup” area and explore “Administrative Formats.”
- Hunt for “Windows Components” and “Remote Desktop Administrations” in this area.
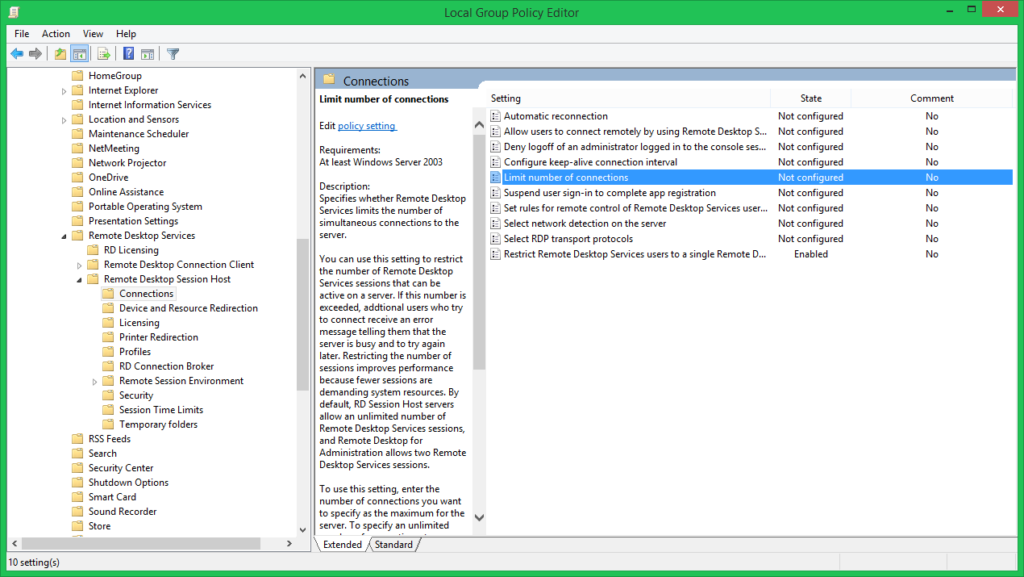
- Adjust policies such as “Limit number of connections” and set them to “Enable multiple remote desktops” with increased connections.
This strategy provides a centralized and scalable approach that is especially useful for more extensive server installations.
3. Terminal Services Configuration:
The Terminal Services Configuration utility provides a graphical interface for configuring RDP. You can get to it with the “tsconfig.msc” command. Navigate to the “Connections” folder within the tool and right-click “RDP-Tcp.” Select “Properties” to change parameters such as the maximum number of connections. This technique provides a more user-friendly interface for administrators who want a visual depiction of configuration changes. To ensure the changes take effect, apply the changes and restart Remote Desktop Services.
Verifying Changes and Troubleshooting:
After allowing numerous Remote Desktop Protocol (RDP) connections on the Windows Server, it’s critical to double-check the modifications to guarantee a smooth and successful setup. Begin by testing distant relations to ensure the enhanced session limit works. Check for any error messages or unusual activity during connection attempts. Troubleshooting is necessary when problems arise. Conflicting group policies, registry issues, or service outages are all common challenges.
Compare settings to the backup made before the alterations to find differences. Use event logs and diagnostic tools to identify faults or anomalies in the RDP setup. This thorough evaluation and debugging procedure guarantees that the server environment stays stable and that administrators may access many RDP connections reliably for increased productivity and effective server administration.
Best Practices and Security Considerations:
Adopting best practices and taking important security measures is required to ensure the security and optimal performance of many Remote Desktop Protocol (RDP) connections on Windows Server.
User Access Controls:
Implement stringent user access restrictions to limit access to only authorized people. Assign users to security groups depending on their jobs and regularly evaluate and change these access rights. This aids in the prevention of unlawful access and the maintenance of responsibility.
Network Security:
Use secure network techniques such as Virtual Private Network (VPN) connections or other private communication methods to ensure network security. Encrypt RDP communication with protocols such as TLS/SSL to safeguard data during transmission and prevent hostile actors from intercepting it.
Regular upgrades:
Keep the server operating system, RDP software, and security programs up to speed with the latest patches and upgrades. Regular updates address any vulnerabilities and strengthen the server’s overall security posture.
Monitoring and auditing:
Set up effective monitoring and auditing methods to track RDP sessions and detect unusual activity. Regularly monitor logs for unauthorized access attempts or odd behavior to enable quick reaction to any security concerns.
2FA stands for two-factor authentication:
Add two-factor authentication to RDP access to improve security. This offers additional verification beyond passwords, reducing the danger of unwanted access even if login credentials are stolen.
Firewall Configuration:
Configure firewalls to allow RDP communication from only trusted IP addresses. Restricting access to specified sources aids in the prevention of brute force attacks and illegal access attempts from outside sources.
Backup and recovery:
Back up key server data and configurations regularly to ensure quick recovery during a security breach or system failure. This assures operation continuity and reduces downtime.
Conclusion:
This article enables Windows Server administrators to fully utilize the capabilities of Remote Desktop by allowing multiple RDP connections. Administrators may tailor their server environment using Registry Editor, Group Policy Configuration, and Terminal Services Configuration to fulfill various purposes. Vigilant verification, troubleshooting, and best practices provide a secure and efficient setup. Accept the expanded capabilities of numerous RDP connections, facilitating faster server management and unleashing a new level of freedom for remote administration on Windows Server.






Leave a Comment
You must be logged in to post a comment.